Full-Spectrum Detection. Automated Response. Built-In Compliance.
GUARDIENT® is an enterprise-grade XDR, SIEM, SOAR, and GRC platform — purpose-built to unify detection, response, and compliance into one continuous security engine. No tool sprawl. No gaps. Every threat detected, every response automated, every control mapped.
Your environment doesn't stop at the firewall.
Your platform shouldn't either.
Modern threats don't respect operating system boundaries or cloud providers. Yet most security platforms are built around a single OS, a single cloud, or a single use case. GUARDIENT® was engineered from the ground up to cover your entire environment — wherever it lives.
Disconnected Tools Create Blind Spots
The average organization runs 6–10 security tools that don't talk to each other. Gaps between your EDR, SIEM, and GRC aren't a process problem — they're an attack surface.
GUARDIENT® solves it: One platform replaces the stack. XDR, SIEM, SOAR, and GRC run natively together — correlated, not cobbled.
SIEM Noise Is Drowning Your Team
Legacy SIEMs ingest everything and prioritize nothing. Analysts spend hours chasing false positives while real threats go unnoticed.
GUARDIENT® solves it: AI-assisted alert enrichment and MITRE ATT&CK–mapped detection rules surface only the signals that matter — with full context already attached.
Manual Response Doesn't Scale
When a threat is confirmed, every minute of manual investigation is a minute attackers use to move laterally through your environment.
GUARDIENT® solves it: SOAR playbooks trigger automatically at detection — isolating endpoints, blocking IPs, opening cases, and escalating to analysts with full forensic context already loaded.
Your Analysts,
Backed by AI
When GUARDIENT® surfaces a critical alert, it doesn't hand your analyst a raw event and a blank screen. That alert is automatically submitted to an AI enrichment layer — powered by ChatGPT — that returns threat context, likely attack classification, and a prioritized list of recommended next steps before the analyst opens the case. Less research time. Faster decisions. Better outcomes.

Four Disciplines.
One Platform. Zero Gaps.
GUARDIENT® delivers enterprise-grade XDR, SIEM, SOAR, and GRC as a single cloud-native platform — not a bundle of acquired tools with paper-thin integrations. Every module was designed to work together from day one.
Cloud-Native · No Rip-and-Replace- Agent-based EDR for Windows, Linux, and macOS
- Agentless cloud workload coverage across AWS, Azure, and GCP
- Network detection via syslog, SNMP, and NetFlow ingestion
- Container and Kubernetes security monitoring
- Vulnerability scanning and exposure management
- Structured and unstructured log ingestion at scale
- Real-time event correlation with AI-assisted behavioral baselines
- MITRE ATT&CK–mapped detection rules
- Threat intelligence feed integration and IOC matching
- Full forensic search and event timeline reconstruction
- Pre-built and custom automated response playbooks
- Endpoint isolation, IP blocking, and account lockdown
- Native ticketing and case management workflows
- Escalation routing with full incident context attached
- Playbook-to-GRC linkage for continuous compliance validation
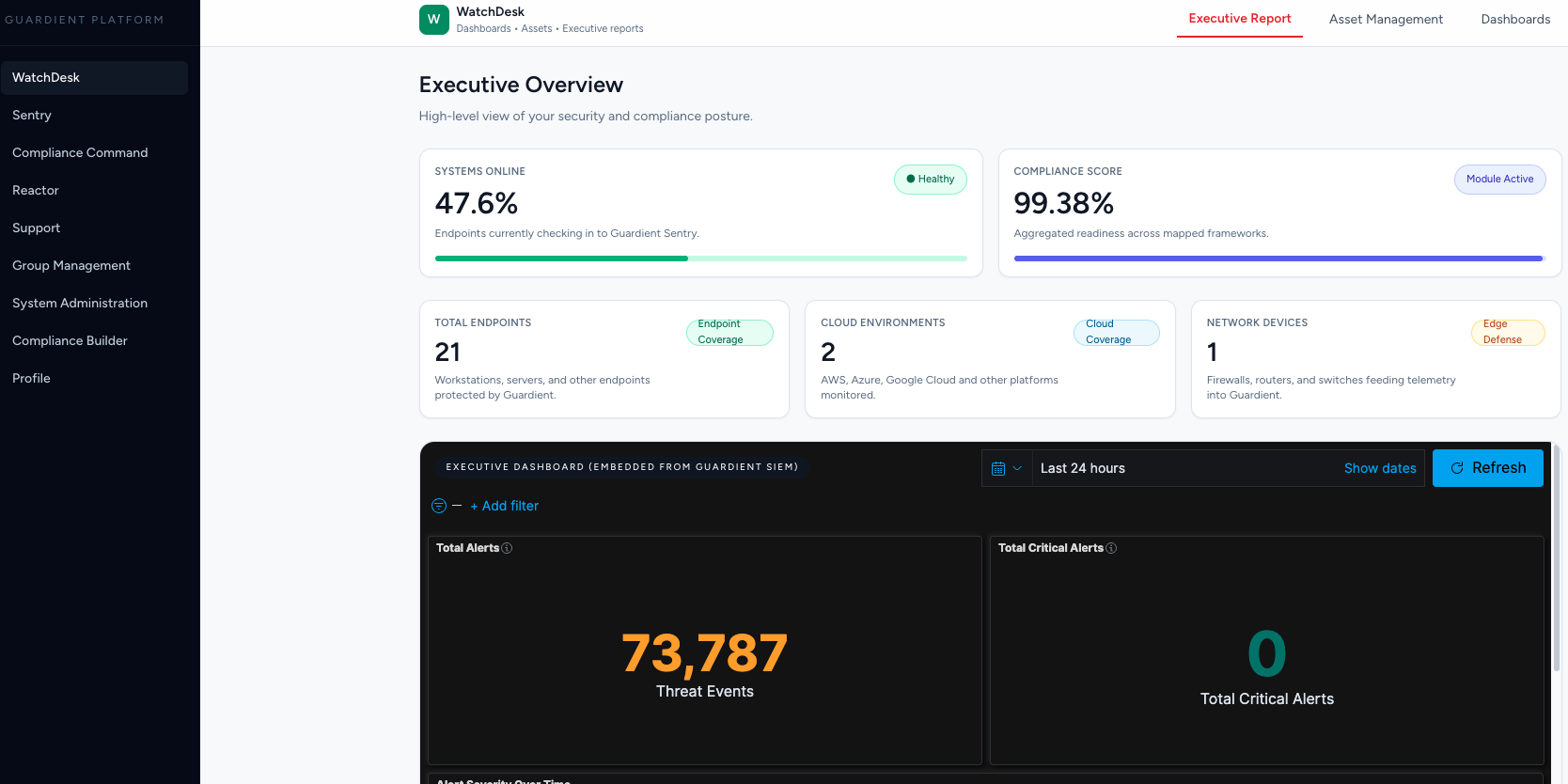
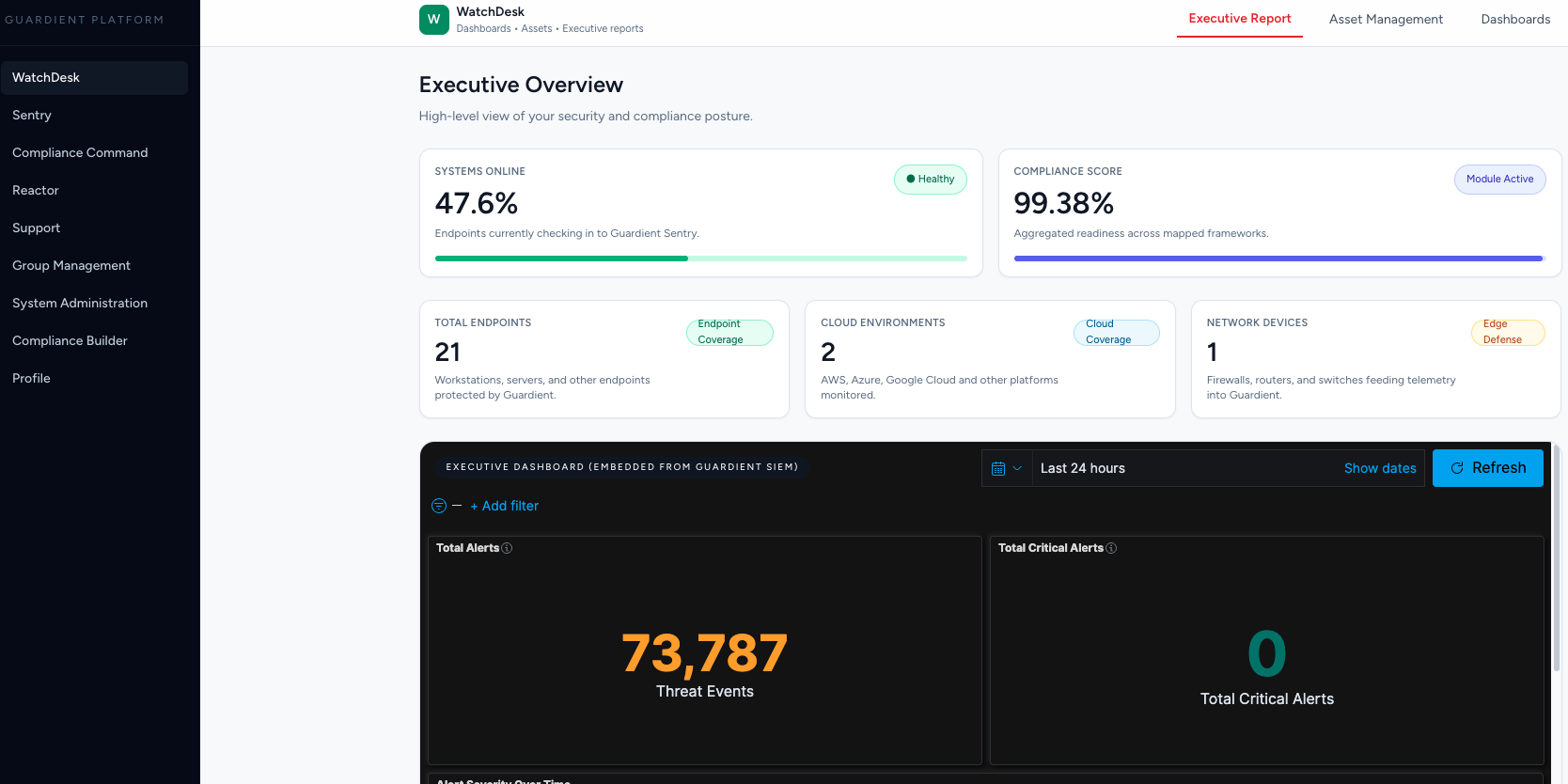
- Single pane of glass across all platform modules
- Role-based dashboards for analysts, managers, and executives
- Live threat queue with risk-ranked alert prioritization
- Compliance posture dashboards tied to real-time detections
- Multi-tenant support for MSSPs and enterprise deployments
- Continuous control monitoring — not point-in-time audits
- Auto-mapped to CMMC 2.0, SOC 2, NIST 800-171, HIPAA, ISO 27001, and PCI-DSS
- Evidence collection tied directly to security events
- Policy management with version control and attestation workflows
- Audit-ready reporting generated on demand
- OS: Windows, Linux (RHEL, Ubuntu, Debian, CentOS, Amazon Linux), macOS
- Cloud-native: AWS, Azure, GCP — plus hybrid and on-premises
- Network: Cisco, Palo Alto, Fortinet, Juniper, pfSense via syslog and API
- ITSM: ServiceNow, Jira, PagerDuty
- Identity: Okta, Azure AD, Active Directory
Built for the Real World.
Not a Lab.
Most platforms are optimized for one environment. Real enterprise infrastructure doesn't work that way. GUARDIENT® deploys across mixed operating systems, multi-cloud architectures, and heterogeneous network stacks — without requiring a separate tool for each.
GUARDIENT® agents deploy natively on Windows (7 through Server 2025), all major Linux distributions, and macOS. Every OS feeds into the same unified detection pipeline — no separate dashboards, no siloed policies, no OS-specific blind spots.
- Unified policy management across all OS types
- OS-specific detection rules tuned per platform
- Cloud VM coverage for EC2, Azure VMs, and GCE instances
- Container host monitoring for Docker and Kubernetes
GUARDIENT® connects natively to AWS CloudTrail, Azure Monitor, and GCP Cloud Logging — ingesting cloud-native events alongside endpoint and network telemetry. Your multi-cloud and hybrid environments are treated as one coherent environment, not separate silos.
- Cloud-native API ingestion — no agents required for cloud logs
- Identity and access monitoring across cloud IAM providers
- S3, Blob, and GCS data access monitoring
- Cloud resource configuration drift detection
GUARDIENT® ingests telemetry from your network infrastructure via syslog, SNMP, and vendor APIs. Cisco, Palo Alto Networks, Fortinet, Juniper, and pfSense are supported out of the box — giving your SIEM full perimeter and east-west visibility.
- Firewall log ingestion and policy violation alerting
- DNS query monitoring for command-and-control detection
- VPN authentication anomaly detection
- Network flow analysis via NetFlow, sFlow, and IPFIX
Already Running Wazuh?
GUARDIENT® Makes It Infinitely More Powerful.
Wazuh is a best-in-class open-source security platform — and many organizations have invested significant time and resources deploying it. GUARDIENT® doesn't replace that investment. Our GRC and SOAR modules layer directly on top of your existing Wazuh infrastructure, transforming raw detection capability into a fully automated, compliance-ready security operation.
Add Compliance Without Starting Over
Wazuh generates powerful alerts and compliance event data — but turning those events into a continuous GRC posture requires a dedicated compliance layer. GUARDIENT®'s Compliance Command module ingests Wazuh alerts and automatically maps them to your active compliance frameworks.
- CMMC, SOC 2, NIST 800-171, HIPAA, and ISO 27001 auto-mapping from Wazuh event data
- Continuous control monitoring replacing periodic scans
- Evidence packages built automatically from Wazuh detections
- Executive compliance dashboards populated from your existing deployment
Automate the Response Wazuh Can't
Wazuh detects. GUARDIENT®'s Reactor module responds. When Wazuh fires an alert, Reactor intercepts it, scores it for risk, and triggers the appropriate automated playbook — endpoint isolation, IP blocking, ticket creation, analyst notification — all without human intervention.
- Bi-directional integration with Wazuh manager via API
- Playbook triggers mapped to Wazuh rule IDs and severity levels
- Automated active response that extends Wazuh's native capabilities
- Full incident cases created in WatchDesk with Wazuh event context attached
Live in a Day. No Rip-and-Replace.
You keep your Wazuh agents, your rules, your custom decoders. GUARDIENT® connects at the manager level — no re-deployment, no disruption. Most organizations are live within a single business day, with the option to migrate to full GUARDIENT® XDR agents on their own timeline.
- Wazuh manager API integration — agents stay in place
- Existing Wazuh rules and decoders remain unchanged
- GUARDIENT® layers on top — additive, not disruptive
- Optional full XDR agent migration at your own pace
"Already invested in Wazuh? Add GUARDIENT®'s GRC and SOAR layers and go from open-source detection to enterprise-grade compliance and automated response — without touching your existing deployment."
Right-Sized for
Your Business
From essential coverage to full 24/7 managed defense — GUARDIENT® scales with your organization at every stage.
- EDR Agent + XDR Platform
- Threat Detection & Alerting
- Basic Compliance Tools
- Self-Service Dashboard
- Everything in Monitored
- Cloud + Network Monitoring
- Vulnerability Management
- Compliance Dashboards
- Monthly Threat Reports
- Everything in Managed
- 24/7 U.S.-Based SOC
- Threat Hunting & Response
- Click-to-Comply Framework
- Quarterly Strategy Reviews
Detect. Correlate.
Respond. Prove.
From the first signal to final remediation — GUARDIENT® stops threats fast, maps activity to compliance frameworks, and gives you evidence-backed audit readiness at every step.
- Unified telemetry from endpoints, cloud, and network
- Lightweight agent with rapid deployment
- Agentless cloud log ingestion
- Real-time collection at any scale
- AI-assisted behavioral analysis
- MITRE ATT&CK rule engine
- Threat intelligence correlation
- Compliance control auto-mapping
- Automated playbooks trigger instantly
- Endpoint isolation and IP blocking
- AI-enriched case creation
- Real-time analyst escalation
- Evidence auto-mapped to compliance frameworks
- Audit-ready dashboards always on
- Automated reporting and control tracking
- CMMC, SOC 2, NIST, HIPAA, and more
One Platform.
Every Environment.
Total Visibility.
GUARDIENT® gives your security and compliance teams a single command surface spanning every OS, cloud, and network segment in your environment. No tab switching. No manual correlation. One platform that sees everything and acts on anything.
One Platform.
Every Environment.
Always Compliant.
Stop patching together EDR, SIEM, SOAR, and GRC from different vendors. Stop running Wazuh without a compliance layer. Stop managing your cloud, your network, and your endpoints in separate tools. Start running GUARDIENT®.
See GUARDIENT® in Action
A focused walkthrough showing how GUARDIENT® unifies your security and compliance — tailored to your organization's environment and requirements.
